Managing hidden services and autoruns is crucial for enhancing security and performance on Windows machines. On Windows PCs, hidden services, orphaned registry keys, and permissive execution policies can lead to unnoticed vulnerabilities.
Startup Entries and Autoruns
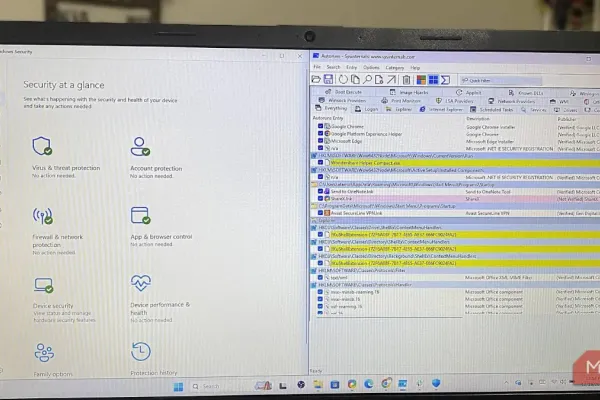
Standard tools like Task Manager show only a fraction of autostart entries. Using Autoruns from the Sysinternals Suite, users can uncover hundreds of hidden registry locations and filesystem hooks. Many startup entries may point to deleted files, allowing malicious software opportunities for exploitation. Autoruns can identify and remove unnecessary entries that Task Manager might miss.
Persistent Services
Windows services often run with elevated privileges, persisting long after the software is no longer needed. Users can manage these services by opening the 'Run' dialog, typing 'msconfig', and adjusting settings in the Services tab. Opting to change the startup type to 'Manual' instead of directly deleting services allows flexibility and helps maintain system integrity.
Scheduled Tasks and Listeners
Scheduled tasks can execute without user consent, often due to applications or telemetric tools. By using PowerShell commands like 'Get-ScheduledTask', users can list and manage tasks that were not disabled. Additionally, 'netstat' can help identify network listeners, mapping active ports to executables and revealing potentially unnecessary exposure on networks.
Execution Policies and Permissions
Permissions granted during installations are rarely revoked automatically by Windows, leading to potential security risks. Checking PowerShell execution policies and reviewing shell extensions ensures that only necessary binaries retain administrative rights, mitigating long-term vulnerabilities.
Regular audits of startup entries, services, and permissions enhance security, working alongside built-in Windows protections. By actively managing hidden elements, users can maintain both trust and control over their PCs.

Comments (0)