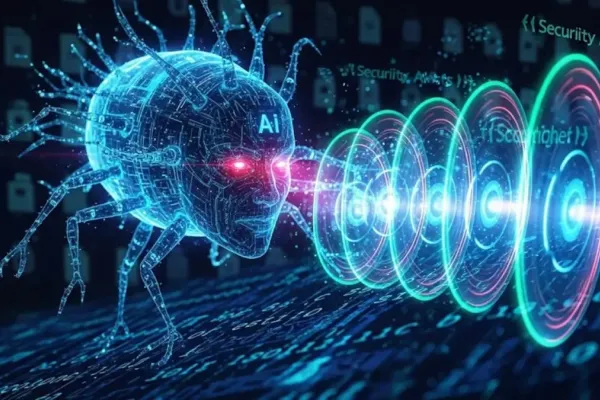
In a significant security development, Microsoft has addressed a critical zero-day vulnerability in the Kerberos authentication system within Windows Server 2025. Disclosed initially in May, the flaw is connected to the handling of domain Managed Service Accounts (dMSAs), particularly through the msds-ManagedAccountPrecededByLink attribute.
Security experts emphasize the urgency of applying this patch—now part of August's Patch Tuesday—due to the existence of exploit code in the wild. The vulnerability allows high-privileged attackers to exploit a relative path traversal flaw, potentially enabling them to impersonate users with higher privileges. This undermines Kerberos delegation in
Impact on Enterprise Systems
The flaw's impact is extensive, affecting domains running Active Directory Domain Services on Windows Server 2025. Systems utilizing dMSAs are particularly exposed, with exploitation requiring certain dMSA attributes and high-level privileges. Despite these prerequisites, many organizations may still be at risk as these accounts are commonly used.
This vulnerability could serve as a critical component in sophisticated attack chains, prompting security vendors to advocate for immediate patching. Beyond the Kerberos issue, the August Patch Tuesday update also covers 107 other vulnerabilities.
Broader Security Concerns
Among the various fixes are critical patches for software like Microsoft Office and
In light of these security threats, organizations utilizing AI technologies through platforms like Azure OpenAI and GitHub Copilot are advised to conduct a thorough inventory of their AI usage. This should be followed by evaluating exposure levels and prioritizing patches based on the degree of access and potential impact.