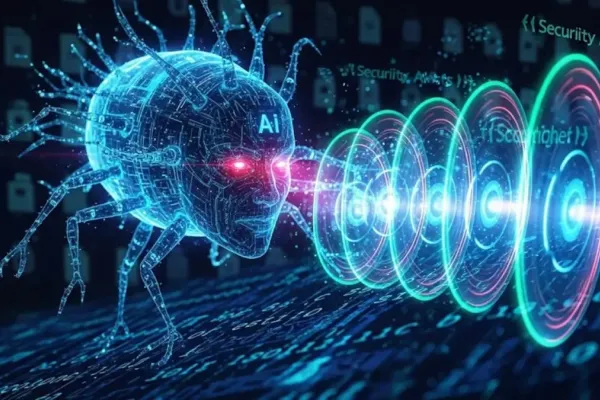
Developed with growing sophistication, EDRKillShifter is reportedly making waves among cybersecurity circles. The latest iteration, observed by researchers at Sophos, represents a significant challenge to endpoint detection and response (EDR) systems and antivirus programs from notable vendors like Sophos, Bitdefender, and Kaspersky.
A New Approach to Security Breaches
This advanced tool is being actively shared and utilized by various ransomware groups. By leveraging obfuscation and anti-analysis techniques, alongside packing services such as HeartCrypt, attackers can cunningly infiltrate security systems. A striking method employed involves embedding malicious code into legitimate applications, like Beyond Compare's Clipboard Compare utility.
One of the most noteworthy aspects of this development is the use of signed drivers in some instances. While previous versions of EDRKillShifter relied on deploying vulnerable drivers, this evolved version adopts a more insidious approach. It locally modifies legitimate executables to insert malicious code, enabling them to operate discreetly once attackers have gained access. This also facilitates the creation of malicious software packages which mimic the appearance of legitimate applications.
Defensive Measures
In response to these evolving threats, experts recommend specific measures to enhance system defenses. The importance of enabling tamper protection on security products cannot be overstated. Additionally, practicing strong Windows role hygiene is vital to prevent privilege escalation, a common exploit method leveraged by attackers.
Security firms are also advocating for the regular updating of systems. As old signed drivers are being de-certified, keeping systems current ensures they remain resilient against such deceptive tactics. Sophos and its counterparts continue to monitor these advances closely, adapting their protective measures in pursuit of robust cybersecurity solutions.
With EDRKillShifter continually evolving, the cybersecurity landscape remains in a state of alert. Organizations are urged to remain vigilant, adopting proactive strategies to safeguard against such incursions.