In a new wave of cyber threats sweeping across India, sophisticated Android malware is increasingly targeting users by masquerading as authentic banking applications. This deception has been noted in a report by CYFIRMA’s threat intelligence team, which highlighted how these malware attacks can thoroughly compromise affected devices.
Android malware poses new threat to users in India
Disguised Delivery Methods
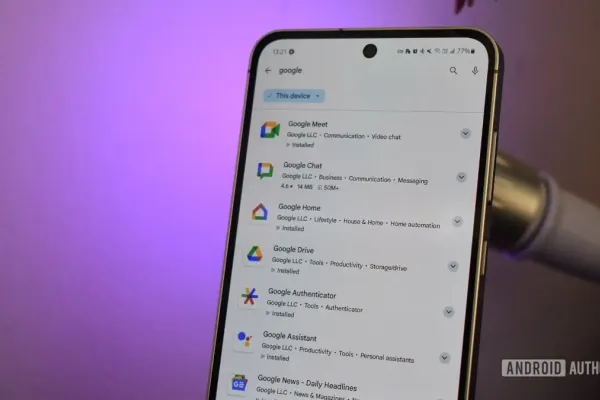
The attacks often commence with the delivery of cleverly disguised droppers. These are malicious applications disseminated through persuasive phishing messages via popular communication channels like WhatsApp, SMS, or email. These phishing APKs are crafted to impersonate system updates or official banking apps, leading users into a false sense of security.
Alarmingly, these APKs also proliferate via malicious QR codes or through counterfeit app stores that closely mimic the official Google Play appearance, making it increasingly difficult for users to distinguish between safe and malicious downloads.
Comprehensive Compromise
Upon installation, the malware seeks broad permissions within the Android system. These permissions are extensive, including capabilities to read and send SMS and intercept two-factor authentication (2FA) codes. Such capabilities grant the malware access to capture sensitive data.
Moreover, to ensure its persistent activity, the malware cleverly circumvents Android’s battery optimization feature, allowing it to remain active in the background indefinitely. It survives device reboots and possesses the ability to manipulate or even conceal notification content. This includes intercepting one-time passwords (OTPs) and banking alerts, all crucial for unauthorized financial transactions without the user's knowledge.
Exfiltration and Control
The captured data, ranging from authentication tokens to valuable SMS communications, are dispatched to a database controlled by the attackers. This remote control grants them potential unauthorized access to users’ sensitive information, thereby amplifying the threat of unauthorized data exposure.
Preventive Measures
The increasing sophistication of these schemes underscores the necessity for vigilance among users. It is critical that users install applications exclusively from certified sources, remain wary of unexpected installation prompts, and meticulously review permission requests. Recognizing and rejecting suspicious activities remain pivotal defenses in countering this persistent mobile threat.