Microsoft Reclassifies Bug as Zero-Day Vulnerability
Microsoft has recently reclassified a previously addressed bug in its September Patch Tuesday update as a zero-day vulnerability. This flaw, designated as CVE-2024-43461, has been exploited by the advanced persistent threat group known as "Void Banshee" since before July. The vulnerability is categorized as a remotely exploitable platform-spoofing issue within the legacy MSHTML (Trident) browser engine, which Microsoft retains in Windows for backward compatibility.
Affects All Supported Windows Versions
This vulnerability impacts all supported versions of Windows, granting remote attackers the ability to execute arbitrary code on affected systems. However, for an exploit to be successful, an attacker must persuade a potential victim to visit a malicious webpage or click on an unsafe link.
Initially, Microsoft rated the severity of this flaw at 8.8 on the 10-point CVSS scale when it was disclosed on September 10. At that time, there was no indication that it was a zero-day vulnerability. On September 13, Microsoft revised its assessment, revealing that attackers had been actively exploiting the flaw as part of an attack chain related to CVE-2024-38112, another MSHTML platform spoofing vulnerability that was patched in July 2024. Microsoft stated, "We released a fix for CVE-2024-38112 in our July 2024 security updates which broke this attack chain."
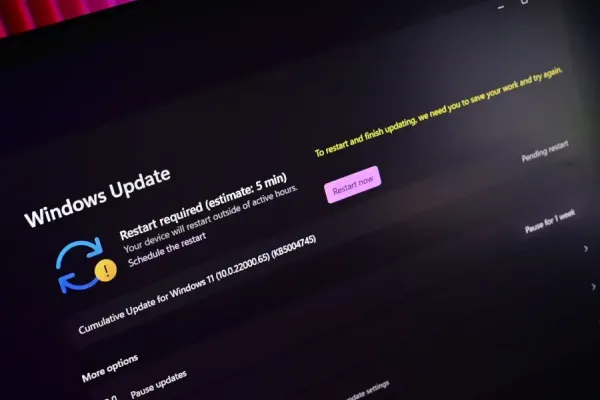
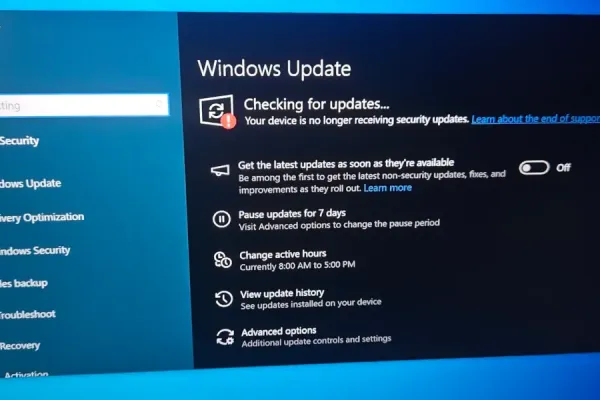
To ensure full protection against exploits targeting CVE-2024-43461, Microsoft urges customers to apply patches from both the July and September 2024 updates. Following Microsoft’s update on September 13, the US Cybersecurity and Infrastructure Security Agency (CISA) added this flaw to its known exploited vulnerabilities database on September 16, setting an implementation deadline of October 7 for federal agencies to adopt the vendor’s mitigations.
Similarities to Previous Vulnerabilities
CVE-2024-43461 bears similarities to CVE-2024-38112, allowing attackers to manipulate user interfaces—specifically, the browser—to display misleading data. Check Point Research, credited by Microsoft for discovering CVE-2024-38112, described the flaw as enabling adversaries to send crafted URLs or Internet shortcut files that, when clicked, would trigger Internet Explorer to open a malicious URL, even if the browser is disabled. Additionally, Check Point noted that threat actors have employed a novel tactic to disguise malicious HTML application (HTA) files as harmless PDF documents during their exploits.
Trend Micro’s Zero Day Initiative (ZDI), which also claims credit for discovering CVE-2024-38112, reported that Void Banshee has exploited this vulnerability to deploy the Atlantida malware on Windows systems. In their observations, Trend Micro noted that the threat actor lured victims with malicious files masquerading as book PDFs, distributed through Discord servers, file-sharing websites, and other channels. Void Banshee is recognized as a financially motivated threat actor, targeting organizations across North America, Southeast Asia, and Europe.
A Two-Bug Microsoft Attack Chain
According to Microsoft’s updated advisory, attackers have been utilizing CVE-2024-43461 as part of a coordinated attack chain that also involves CVE-2024-38112. Researchers at Qualys previously indicated that exploits targeting CVE-2024-38112 would be equally effective against CVE-2024-43416, given their near-identical nature. Peter Girnus, a senior threat researcher at ZDI credited for CVE-2024-43461, explained that attackers leveraged CVE-2024-38112 to navigate to an HTML landing page through Internet Explorer using the MHTML protocol handler within a .URL file. "This landing page contains an HTML which downloads an HTA file where attackers can execute arbitrary code," Girnus elaborated.







Comments (0)
Создание новых комментариев временно недоступно.